In March 2026, I discovered a privilege escalation vulnerability in Azure Backup for AKS that allowed a user with only the “Backup Contributor” Azure role (zero Kubernetes permissions) to gain cluster-admin on any AKS cluster.
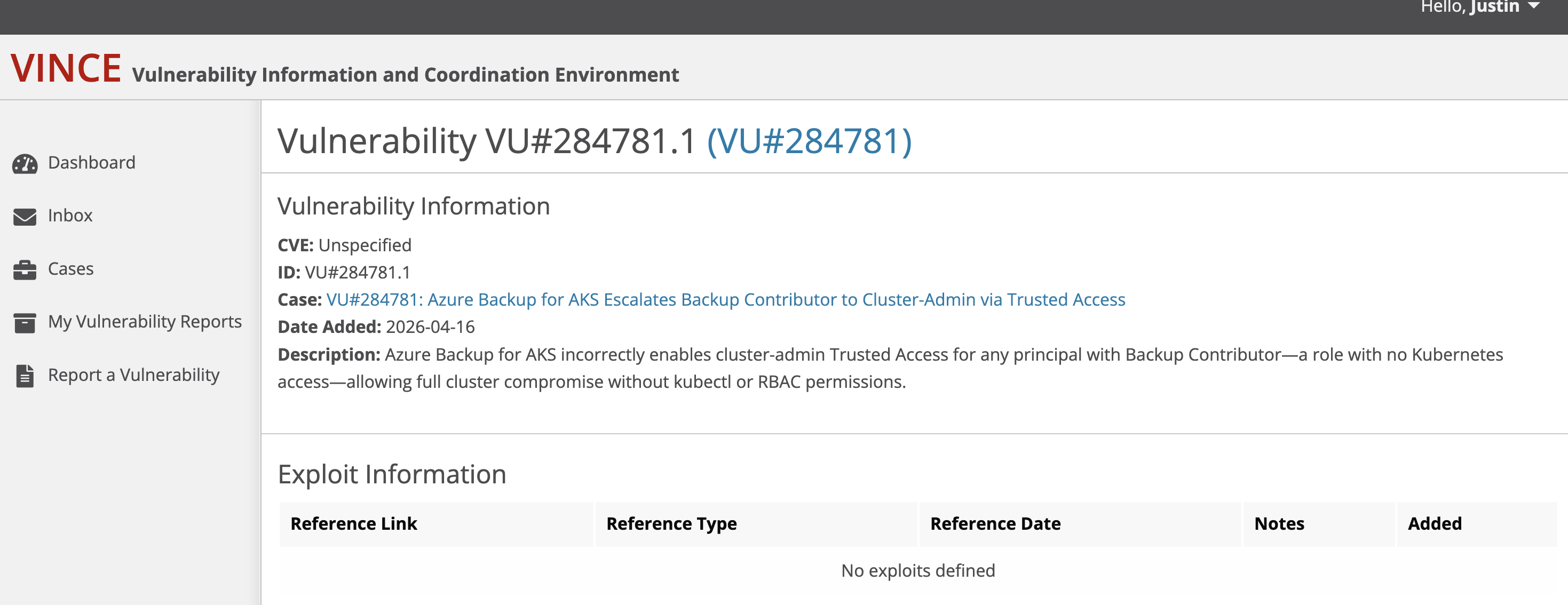
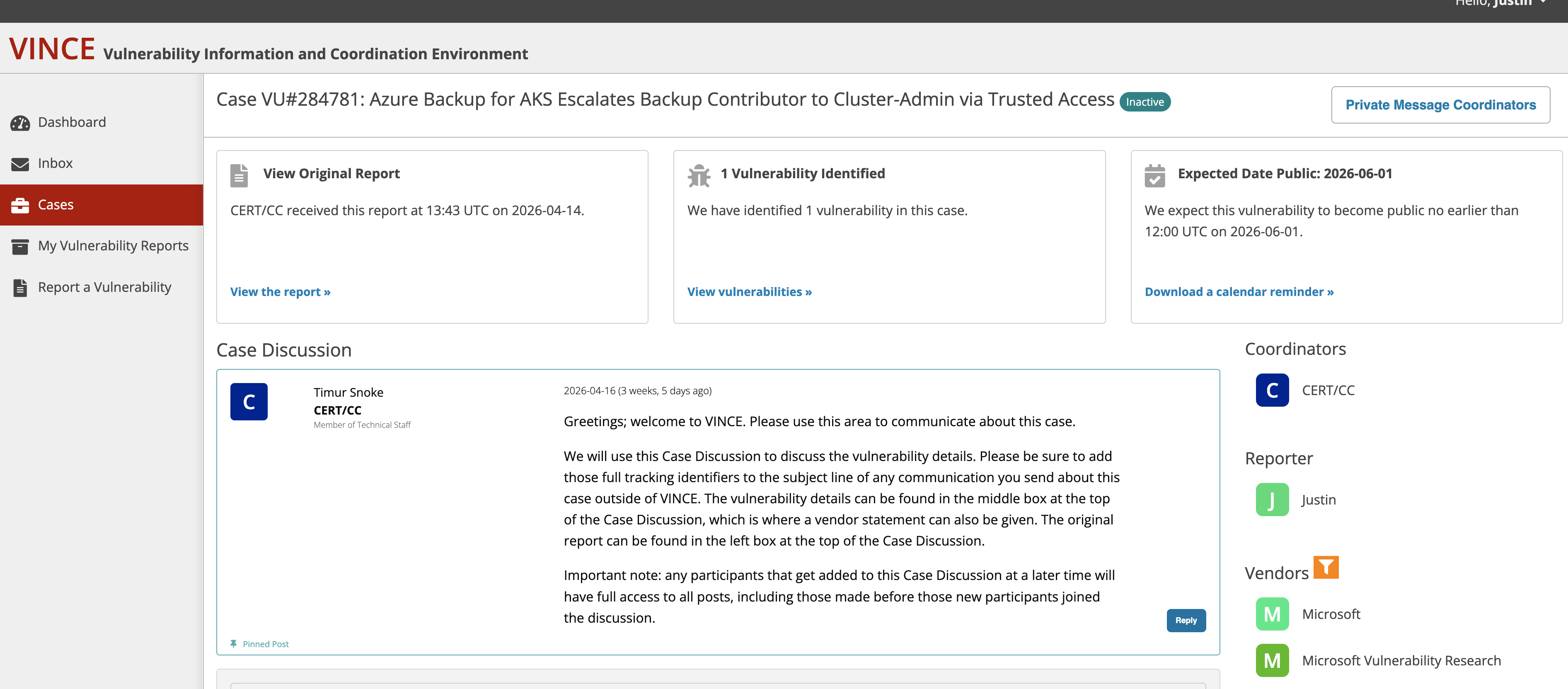
CERT/CC validated this finding as VU#284781 on April 16, 2026.
Microsoft rejected it, claiming the “attacker already held administrator access.” This was factually incorrect — the vulnerability grants cluster-admin, it does not require it.
On May 12, 2026, I confirmed Microsoft has silently patched the behavior without:
- Assigning a CVE
- Publishing a security advisory
- Notifying affected customers
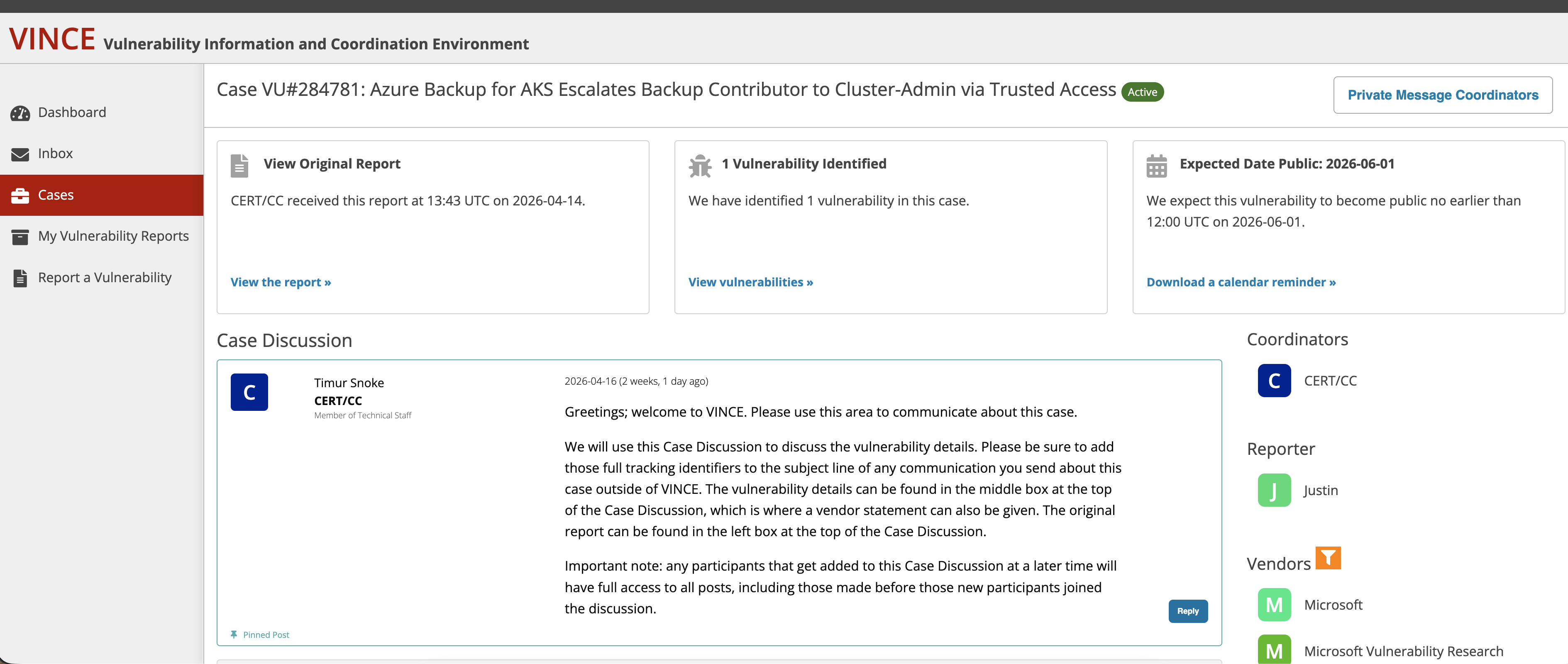
CERT/CC Validation
CERT/CC independently validated this vulnerability and assigned VU#284781. The case was scheduled for public disclosure on June 1, 2026.
Microsoft’s CVE Rejection
On May 4, 2026, Microsoft’s Lisa Olson emailed MITRE recommending no CVE be assigned. The email contains a false claim that “the attacker already held administrator access to the cluster.”
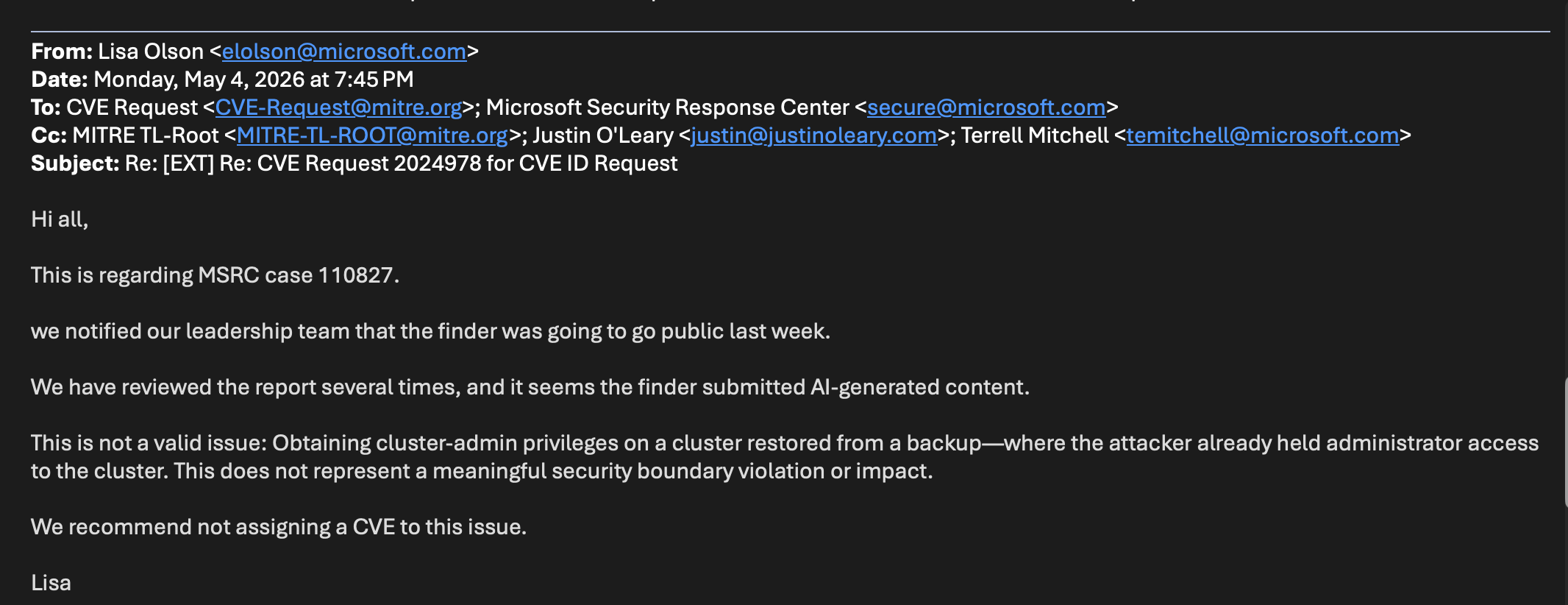
This is factually incorrect. The vulnerability allows a user with zero Kubernetes permissions to gain cluster-admin. The attack does not require existing cluster access — it grants it.
Microsoft also claimed the report was “AI-generated content” — an ad hominem deflection that does not address the technical validity of the finding.
CERT/CC Case Closure
Two days later, on May 6, 2026, CERT/CC closed the case, citing CNA hierarchy rules.
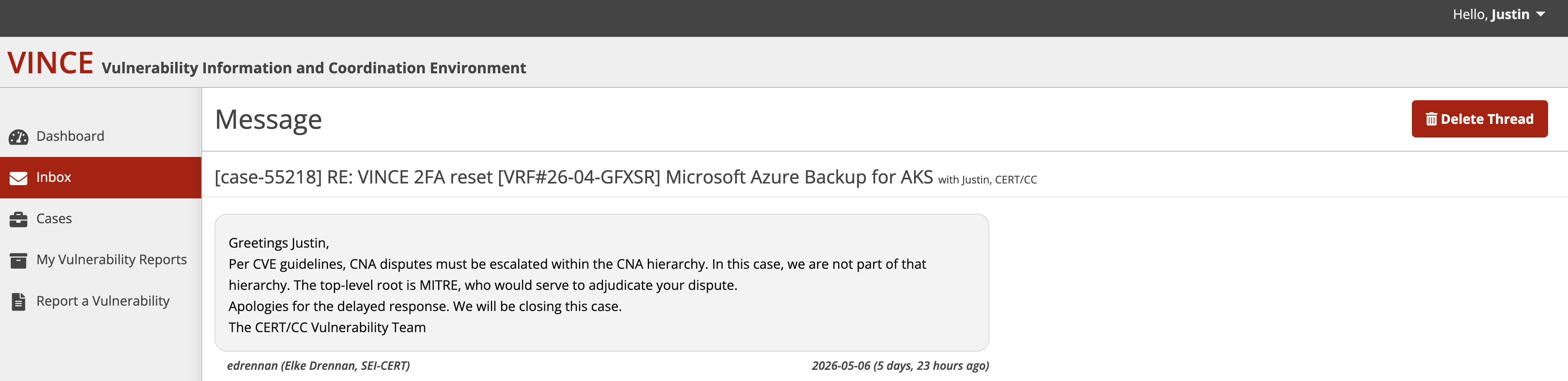
The closure came despite CERT/CC having already validated the vulnerability and assigned VU#284781. The case remains marked as INACTIVE in VINCE:
Vulnerability Details
Azure Backup for AKS uses Trusted Access to grant the backup extension cluster-admin privileges. The vulnerability allowed a user with only Backup Contributor (an Azure RBAC role with zero Kubernetes permissions) to trigger this access grant.
Attack chain:
- Attacker has Backup Contributor on backup vault (no K8s access)
- Attacker enables backup on target AKS cluster
- Azure auto-grants Trusted Access with cluster-admin
- Attacker extracts secrets via backup or restores malicious workloads
This crossed the trust boundary between Azure RBAC and Kubernetes RBAC — a Confused Deputy vulnerability (CWE-441).
CVSS 3.1: 9.9 (AV:N/AC:L/PR:L/UI:N/S:C/C:H/I:H/A:H)
Evidence of Silent Patch
Current behavior returns errors that did not exist in March 2026:
ERROR: UserErrorTrustedAccessGatewayReturnedForbidden
"The Trusted Access role binding is missing/has gotten removed"
ERROR: UserErrorMissingVaultMSIReaderPermissionsOnCluster
"Backup Vault managed identity requires Reader role on the cluster"
These validation checks were added silently. The original attack path is now blocked.
Timeline
| Date | Event |
|---|---|
| 2026-03-17 | Reported to MSRC (Case 110827 / VULN-178608) |
| 2026-03 | MSRC rejected with false claim |
| 2026-04-14 | Submitted to CERT/CC |
| 2026-04-16 | CERT/CC validated as VU#284781 |
| 2026-04-16 | CERT/CC scheduled public disclosure for 2026-06-01 |
| 2026-05-04 | Microsoft’s Lisa Olson emails MITRE recommending no CVE |
| 2026-05-06 | CERT/CC closes case citing CNA hierarchy |
| 2026-05-12 | Confirmed silent patch via changed error behavior |
Why This Matters
The coordinated disclosure process failed:
- CERT/CC validated the vulnerability
- Microsoft patched without acknowledgment
- No CVE was assigned
- Customers were never notified
Organizations that granted Backup Contributor between an unknown start date and May 2026 were exposed to privilege escalation. Without a CVE, security teams cannot track this exposure.
Silent patching protects vendors, not customers.
References
- MSRC Case: 110827
- VULN ID: VULN-178608
- CERT/CC: VU#284781 (closed)
- oss-security: Mailing list post